During my recent visit to the Apple store, I saw Apple experts demonstrating an iPad to a group of kids and their parents. I increasingly see kids holding iPads instead of toys. An iPad is expensive, and fragile. I was curious see how a 2-year old could use an iPad. Most importantly, I was also curious to see if an iPad App was simple to use for a kid.
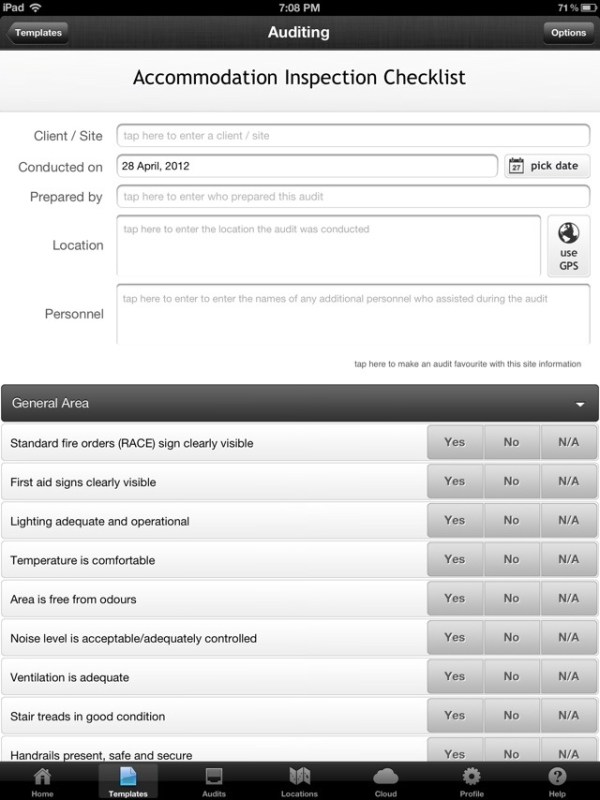
I downloaded Crayola Paint and Create – a free App for the iPad. I was interested in studying the features, user interface, user interaction, and the overall user experience. This is how the App looks:

The main elements were Coloring Pages, Fun Activities and Free Draw. I decided to use Coloring pages and color a drawing:
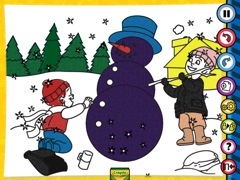
I clicked the Crayola icon at the bottom of the screen to display various types of crayons with different colors. You can see the following icons on the right: Pause (to pause the movements like snow falling or pause other interactive elements), Undo, Redo, New, Settings, Share (to share via email or on Facebook), Help, and Exit.

This is how a partially colored coloring page looks:

I could easily use different colors and fill different parts of the page with solid colors. This is how a fully colored page looks:
The app is configured to use a finger by default. There is also a setting to use an iMarker instead of a finger (an iMarker is like a pencil that can be used with the iPad). Obviously, the Help and Settings are a little complicated for kids since they may not be able to read. Apart from Help, Settings, and Share, the other options were extremely easy to use.
What is Apple’s strategy to promote iPads for kids by launching a Kids Corner in the Apple store? What is the value proposition for parents to purchase such and expensive device for their kids? Here’s what I think:
Get an Apple user for life – That’s right. Catching them young will ensure they are Apple users for life! Kids will never choose an Android device or another tablet if they are introduced to the iPad at the age of 2. Apple’s strategy of catching users at a very young age will lead to huge revenue for years to come.
Reduce cost per user – The cheapest iPad costs approximately 400$. If a family of four – two parents and two kids use an iPad, the cost of buying an iPad is divided by 4. Although families do not use terms like Cost per User to decide whether to buy an iPad, they definitely calculate it sub-consciously.
Tap a new market segment – Kids are a huge market segment – not just for games, but also in the field of education. Tapping this market segment leads to a huge revenue for Apple.
Use kids to market the iPad and Apps – I was amazed to see how Apple was using kids to market the iPad. With the Share option, kids could share their coloring pages with their friends (the parents might share it for them). Other kids looking at these colorful pages would want to do the same. Not only is Social Media being introduced at a very young age, the iPad is being marketed via Word of Mouth (the most powerful way to influence prospective buyers).
Save money for families and schools – Families and schools can save money on paper, crayons, and other consumables required on a daily basis.
A safer option – Kids (at home or in Pre-K) eat crayons that may be harmful for their health. Since the crayons on an iPad are electronic, it is very safe for kids.
Save the environment – Reducing the usage of paper obviously save trees.
Crayola Paint and Create gave me great insights to Apple’s strategy. I could also envision the future – where most of the interaction happens through touch screens instead of keyboards. It also helped me realize that language will never be a barrier for user interaction since expressive icons are a great way to communicate with the user. Intelligence, knowledge, skills, language, and education will never be a barrier for users in the world of touch screens.
Hello kids, welcome to the iWorld!